Data availability layers (DALs) have become the backbone of modular blockchain innovation, but a new paradigm is rapidly gaining momentum: permissionless multi-dimensional consensus. This approach is not just another incremental upgrade - it represents a leap forward in how blockchains can achieve scalability, security, and decentralization all at once. As permissionless blockchains like Bitcoin and Ethereum continue to push boundaries, the need for more robust, flexible consensus mechanisms has never been clearer. Enter the era of multi-dimensional consensus, where multiple resources and validation strategies work in concert to create resilient, high-throughput networks.
Why Single-Dimension Consensus Is No Longer Enough
Traditional blockchains typically rely on a single consensus mechanism - Proof-of-Work (PoW) or Proof-of-Stake (PoS) - to validate transactions and secure their networks. While these models have proven effective at bootstrapping decentralized ecosystems, they each have inherent tradeoffs. PoW offers strong security but consumes significant energy; PoS reduces environmental impact but can concentrate power among large stakeholders. Relying on just one resource or validator type exposes networks to targeted attacks and limits scalability as usage grows.
This is where multi-dimensional consensus protocols, such as the innovative Minotaur protocol, step in. By combining resources like computational work and staked tokens within a single framework, these protocols make it exponentially harder for adversaries to compromise the system. Validators can participate using different resource types - computation, stake, or even new forms of economic collateral - leading to better resource utilization and more inclusive participation.
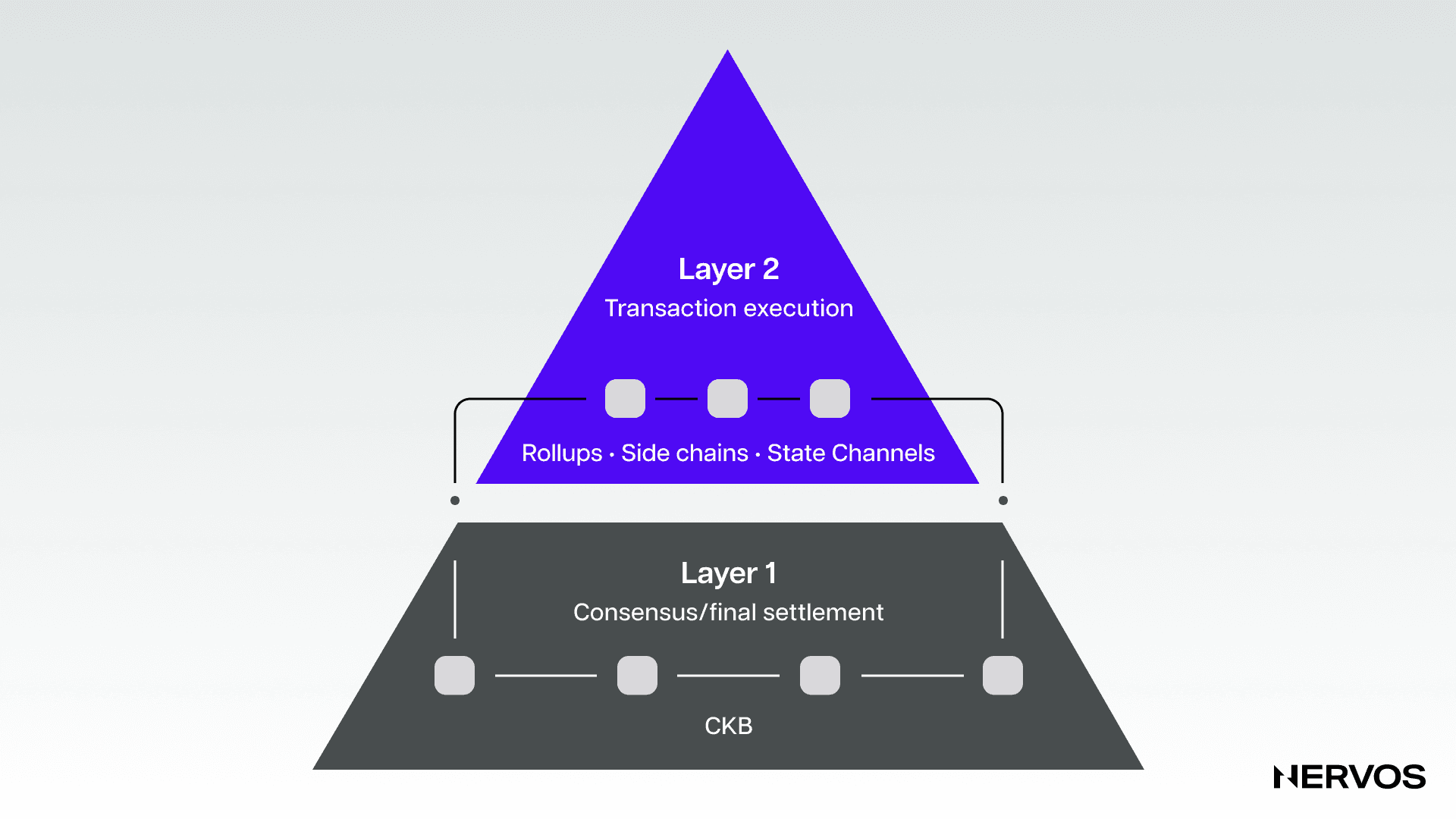
The Modular Blockchain Revolution: Decoupling Data Availability
The rise of modular blockchain architectures has shifted how we think about protocol design. Instead of monolithic chains that bundle execution, settlement, and data availability together, modern systems are separating these concerns into specialized layers. The Celestia data availability layer is a prime example: it provides scalable data availability that any execution environment can plug into for secure transaction posting.
But even the best DA layers face challenges when built atop single-resource consensus models. Permissionless multi-dimensional consensus unlocks new possibilities for DALs:
Key Advantages of Permissionless Multi-Dimensional Consensus
- Enhanced Security: Combining multiple consensus mechanisms (e.g., Proof-of-Work and Proof-of-Stake) makes it significantly harder for attackers to compromise the network, as they must control several resource types simultaneously.
- Improved Scalability: By distributing validation across diverse resources, multi-dimensional consensus protocols enable data availability layers to handle higher transaction throughput without bottlenecks.
- Greater Decentralization: Permissionless participation across multiple resource types (such as computational power and stake) lowers entry barriers and encourages a more diverse set of validators, reducing centralization risks.
- Resource Optimization: Leveraging the strengths of different consensus mechanisms allows for more efficient use of network resources, balancing energy consumption and economic incentives.
- Resilience Against Diverse Attacks: Multi-dimensional consensus increases network robustness by requiring an adversary to exploit several consensus layers, rather than just one, to disrupt data availability.

By integrating multiple validation resources at the base layer, projects like Celestia and Avail are pioneering solutions that can handle massive transaction throughput while maintaining permissionless access for validators worldwide.
Pushing Scalability Without Sacrificing Security
What makes this new paradigm so compelling? For one thing, it addresses two perennial blockchain bottlenecks: throughput and decentralization. Multi-dimensional consensus allows DALs to distribute validation workloads more efficiently across diverse resources, supporting higher transaction rates without centralizing control among a handful of actors.
This approach also greatly strengthens network resilience. Attackers must now compromise multiple independent resource pools simultaneously - an order-of-magnitude harder task than targeting a single validator set or mining pool. For users and developers building atop these DALs, this means greater confidence that their data will always be available and verifiable by anyone in the world.






No comments yet. Be the first to share your thoughts!